

AVG Rescue CD GNU/Linux is a free product of AVG Technologies and there is no explicit support for it. Fortunately you can use a free forum provided by AVG Technologies for their free products. You can report your bugs, problems and questions there. There is no guarantee for a quick reply or bug fix from AVG's side, but, hopefully the community of free users will be able to provide you with a quick and an accurate response. The forum for the rescue CD is accessible here.
After booting from the CD, you will be asked to accept the End User License Agreement (EULA).
Note: you can run the entire process remotely, if you wish, using
Secure Shell (SSH) from
another system, if you follow the steps further down in this document for
resetting the root password and starting the process from a
shell prompt
using the arl command.

After you accede to the license agreement, the Microsoft Windows partitions on the hard drive in the system will be mounted.

After the Windows partitions are mounted, you will be asked whether you want to update the software. Accept the default option of "yes" by hitting Enter, which will get you the latest antivirus definitions.

Note: you can maneuver through options you will see presented to you by using the cursor keys on the keyboard.
You will then be prompted as to the type of update to perform. You have the following choices:
| Online | Update from the Internet. |
| Offline | Update from directory. |
| Download | Download update files from the Internet. |
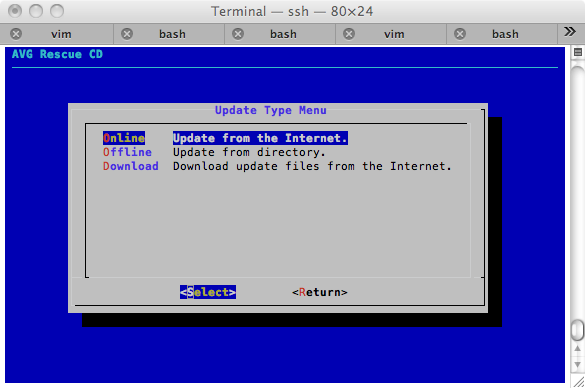
You can just hit Enter to get the latest updates, if the system has an active Internet connection.
You will next be prompted as to whether you want a "Virus database update", "Program update", or "Optional update." The default option is "Virus database update", which will include the other updates, so you can just hit Enter to accept the default option.

When the update is completed, you will be prompted to hit Enter to continue.

You will then be presented with the AVG Rescue CD main menu. You can just hit Enter, if you wish to start scanning the system.

If you wish to see the version of ARL, you can select "About".

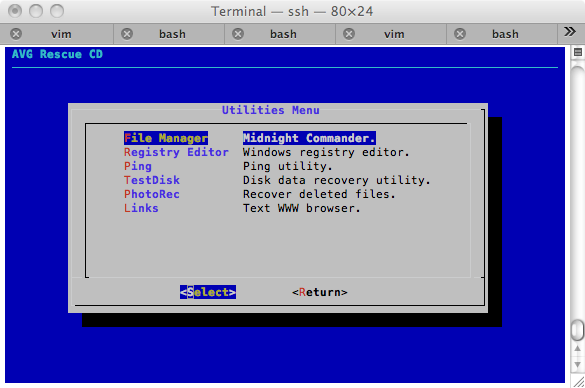
The "Utilities" option shows the following utitlities list.
| File Manager | Midnight Commander. |
| Registry Editor | Windows registry editor. |
| Ping | Ping utility. |
| TestDisk | Disk data recovery utility. |
| PhotoRec | Recover deleted files. |
| Links | Text WWW browser. |
When you are ready to scan the system and have selected the "Scan" option, you will be asked whether you wish to scan volumes or a directory. If you wish to scan the entire hard drive where Microsoft Windows is located, just hit Enter with the default selection of "Volumes".

You will then see a "Scan Volumes" menu with all volumes selected. The
hard drive partitions will be in the form /mnt/sda1,
mnt/sda2, /mnt/hda1, etc. depending on how many
partitions
are on the hard drive and the type of drive. I would suggest deselecting the
one that has "iso9660" in the description as that is the CD itself, which
you normally should not have to concern yourself about. You can deslect it
by using the downard pointing arrow key on the keyboard to navigate to it
and then hit the space bar to deselect it. You can then hit
Enter to proceed.

You will then be able to select various scan options.

The following options are available with those marked with an asterisk chosen by default.
| [*] | arc | Scan inside archives. |
| [ ] | pdw | Report password protected files. Use with --arc |
| [ ] | arcbombsw | Report archive bombs. Use with --arc. |
| [*] | heur | Use heuristics for scanning. |
| [*] | pup | Scan for potentially unwanted programs. |
| [*] | pup2 | Scan for enhanced set of Potentially Undwanted Programs. |
| [ ] | coo | Scan cookies. |
| [ ] | hidext | Recognize hidden extensions. |
| [ ] | macrow | Report documents with macros. |
The scanner will not be able to scan password protected files, such
as password protected zip files. You can check the pdw option,
if you want a list of such password protected files included in the scan
results. You can select and deselect options using the space bar.
Hit Enter to start the scan when you have selected the options you want or to accept the default options.
When the scan is completed, you will see a list of the infections found, similar to the following.

When you hit Enter, you will see a scan result menu. You can choose to display the report file, handle each infected file separately, hangle single or group of infected files, rename all infected files, or delete all infected files.

If you choose the "Individual" option, you will be prompted file by file as to whether you wish to skip, rename, or delete the file.

If you choose "Select", instead of "Individual", you will see all infected files selected by default. You can deselect ones you don't want to rename or delete with the "rename all infected files" or "deleted all selected files" options. You can deselect a file by moving to it with the cursor key then deselecting it with the space bar.

If you wish to see details on the infected file, navigate to the "Detail" option with the cursor keys.

Select the "Action" option to proceed, when you are finished deselecting files.

If you have any problems deleting all of the selected files as a group, go back to the individual option and delete them one by one.
When you wish to reboot, you can do it via the menu or you can type
reboot at a shell prompt.
You can get other shell prompts at any time by hitting the Alt key and a function key, such as F2 simultaneously, i.e. Alt-F2. You can return to the primary shell at any time by hitting Alt-F1. If you do so you will see the following:
Welcome to AVG Rescue GNU/Linux arl login:
You can use root for the userid; there is no password prompt.
When the scan is completed, you can get another shell prompt and make the
working directory /opt/avg/arl (AVG stores its
files in the /opt/avg directory) and examine the log file
containing the scan results, which is scan_report.txt
Welcome to AVG Rescue GNU/Linux arl login: root [root@arl ~]# cd /opt/avg/arl [root@arl ~]# more scan_report.txt
The rescue CD runs a Secure Shell server. To log into the system running the AVG rescue CD software using SSH, you will need to change the root password to one of your choosing. You will be warned that a password is too weak or too short, if you don't select a strong password.
[root@arl ~]# passwd root Changing password for root New password: Retype password: Password for root changed by root
You can determine what IP address was assigned to the system by an
Dynamic Host Configuration
Protocol (DHCP) server on your network by using the ifconfig
command.
[root@arl ~]# ifconfig
eth0 Link encap:Ethernet HWaddr 00:07:E9:87:30:B0
inet addr:192.168.0.12 Bcast:192.168.2.63 Mask:255.255.255.192
inet6 addr: fe80::207:e9ff:fe87:30b0/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:15169 errors:0 dropped:0 overruns:0 frame:0
TX packets:720 errors:0 dropped:0 overruns:0 carrier:0
collisions:1 txqueuelen:1000
RX bytes:2371388 (2.2 MiB) TX bytes:61516 (60.0 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
Look for the inet addr. The relevant IP address will normally
be the one associated with eth0. You can then use that address
to establish an SSH connection to the system from another system.
$ ssh root@192.168.0.12 root@192.168.0.12's password: [root@arl ~]#
You can use scp from a remote system to copy the log file
from the scanned system to the remote system.
$ scp root@192.168.0.12:/opt/avg/arl/scan_report.txt . root@192.168.0.12's password: scan_report.txt 100% 5443 5.3KB/s 00:00
If you wish to determine which version of ARL Linux the rescue CD uses,
you can find that in /etc/arl-version
[root@arl ~]# cat /etc/arl-version ARL-110831
You can access the ARL menu by typing arl at a shell
prompt. That will put you at the point where you are asked to accept
the End User License Agreement (EULA).
[root@arl ~]# arl
I sometimes wish to copy all of the infected files to another location
for analysis by other antivirus tools or to upload them to sites such
as Virustotal, which will scan files
for free with multiple antivirus programs. I put all of the files in a .gz
file and then transfer the file to another system. To do so, you can copy
scan_report.txt to another file and then edit that file, so that
it contains only the file names for the infected files. I.e., remove the "virus
identified", "Trojan horse", etc. comments from the end of each line listing
an infected file and remove the comment lines from the beginning and end of
the file. The vi editor is
provided on the CD, so you can use it to edit the file. Once you have removed
the extraneous information from the file, leaving only the file names, put
double quotes at the beginning and end of each line, since the path and/or
filename for some files may contain spaces. You can do so in vi or you can use
the following sed commands at the shell prompt to put
a double quote at the beginning and end of each line.
# sed -i 's/^/"/' infected_filenames.txt # sed -i 's/$/"/' infected_filenames.txt
I then use tar to create an archive file of the infected files.
[root@arl arl]# cat infected_filenames.txt | xargs tar -cvf infected-files.tar
I then compress the file with gzip before transferring it
to another system with scp.
[root@arl arl]# ls -lh *.tar -rw------- 1 root root 32.7M Nov 11 06:36 infected-files.tar [root@arl arl]# gzip infected-files.tar [root@arl arl]# ls -lh *.gz -rw------- 1 root root 69.6K Nov 11 06:42 infected-files.tar.gz
References:
Created: November 11, 2011