

Avira AntiVir Rescue System is a Linux-based application that allows accessing computers that cannot be booted anymore. Thus it is possible to:
The Avira AntiVir Rescue System is updated several times a day so that the most recent security updates are always available.
To use the software, download rescuecd.exe from
Avira AntiVir Rescue System. Just double-click on rescuecd.exe
to burn the rescue system package to a CD or DVD. You can then use this CD or
DVD to boot a PC.
When you run rescuecd.exe you will be prompted to choose
the device which you will use to burn the CD or DVD. The software will choose
your default CD burner.
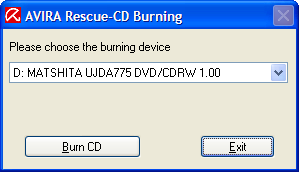
Insert a blank CD or DVD in the device and click on Burn CD. You will see a message indicating "the CD has been created successfully", when the process completes.
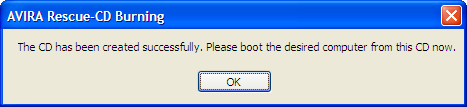
The CD/DVD will be ejected at completion of the burning process. Boot the system you wish to check with the CD/DVD.
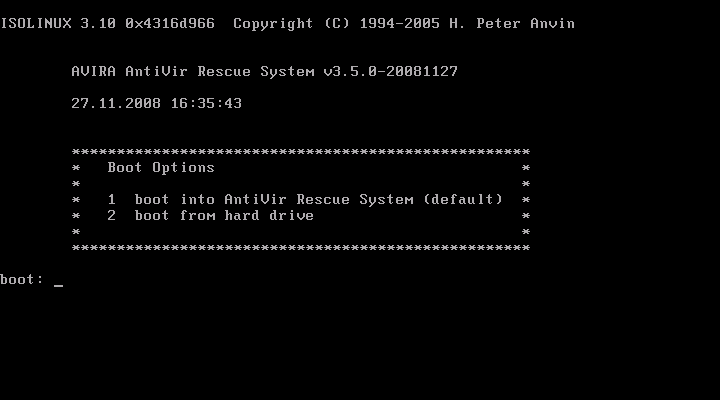
After booting, you will see the bootmanager-menu. You then can choose either to boot from the local hard disc or boot the Avira AntiVir Rescue System from CD/DVD-ROM. Press key '2' to choose "boot into AntiVir Rescue System" and confirm with Enter'. The Avira AntiVir Rescue System will then start.
After you boot the Avira AntiVir Rescue System from the CD, you will see a Graphical User Interface (GUI). The default language used is German. You will see German and British flags in the lower-left hand corner of the screen. Click on the British flag to obtain an English-language interface.

By default, the software will only notify you when it detects files that may be associated with malware. If you wish it to try to repair infected files, or, click on the Configuration button. You can then check "try to repair infected files" and "rename files, if they cannot be removed", if you wish. For the most comprehensive scan, select "scan all files."
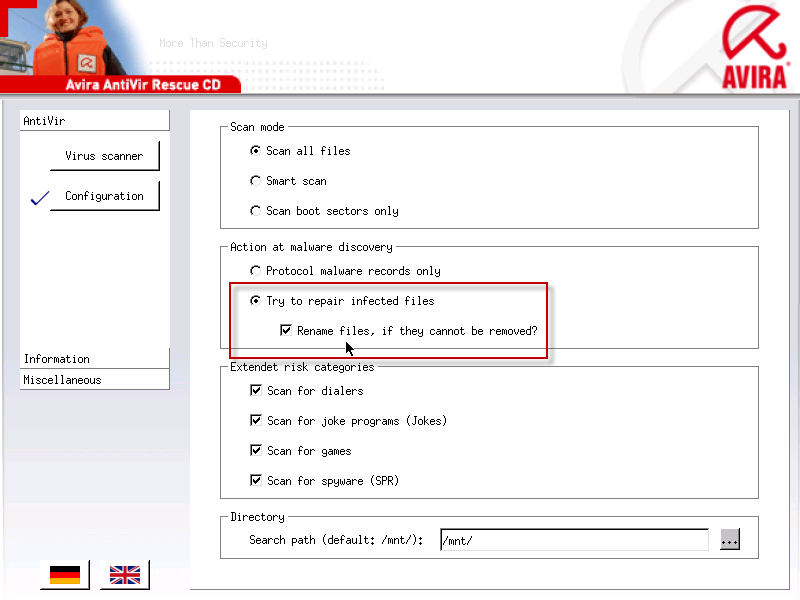
Once you have set the configuration options to your liking, click on the Virus Scanner button and then click on the Start Scanner button to start the scanning process.
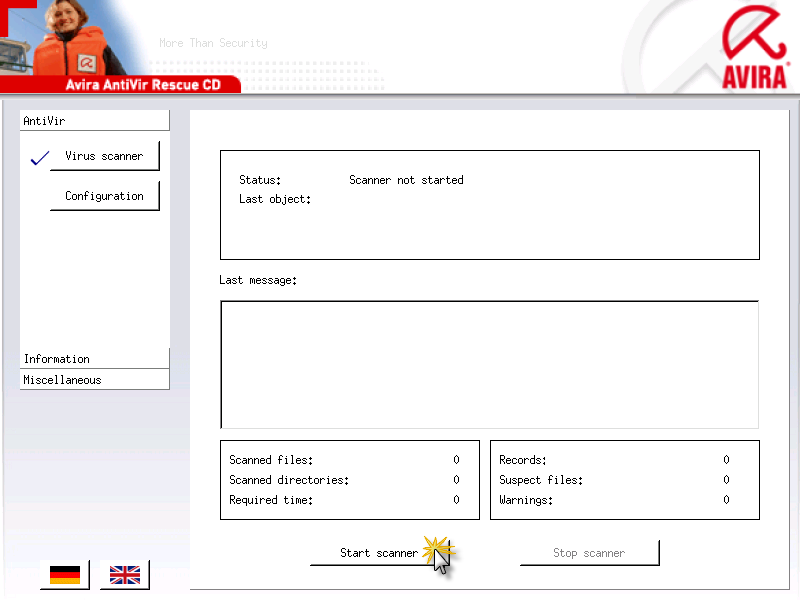
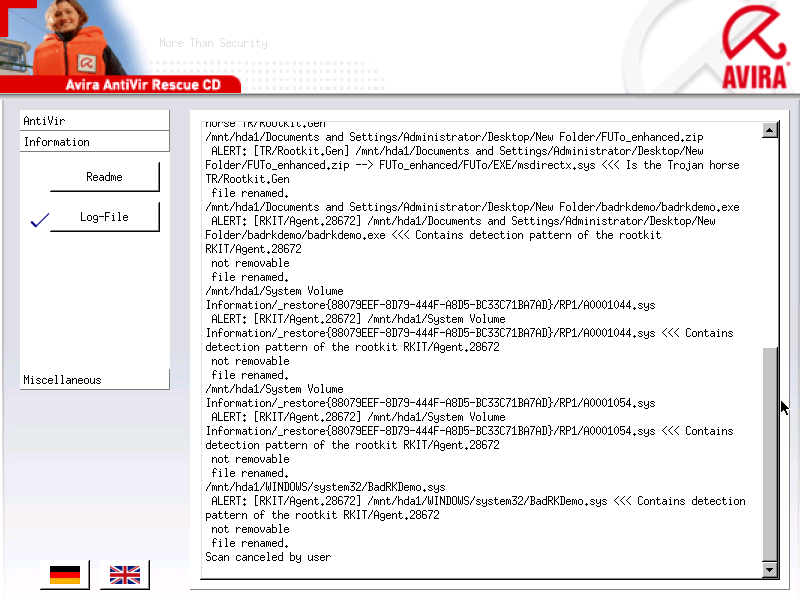
You will see information about what the virus scanner is doing in the "last message" window. Malware that has been detected will be reported in that window. After the scan has been completed, you can also click on the Information button and then the Log-file button to see what was detected.
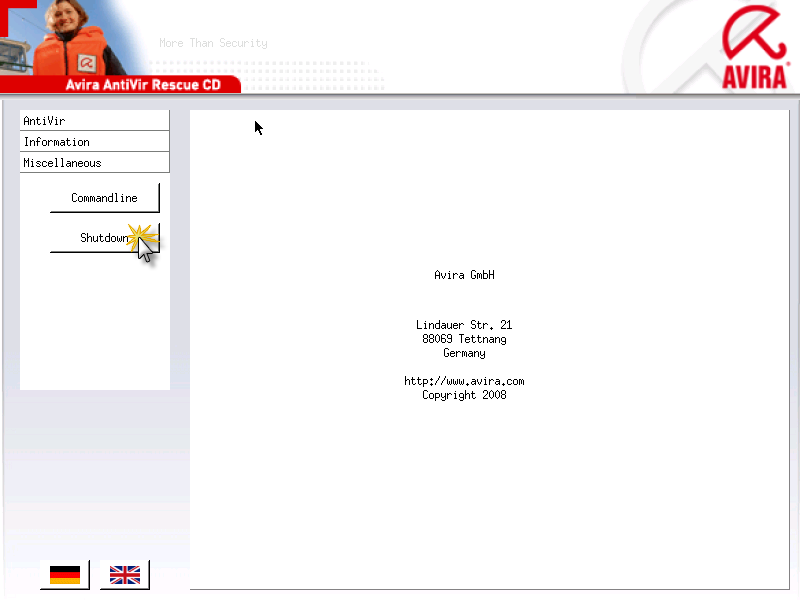
If you clck on the Miscellaneous button, you have the opportunity to obtain a command line interface by clicking on the Commandline button.
When you select that option, you will see an informational message appear indicating you can hit Alt-F7 to return to the graphical user interface.
|
Attention! You are about to switch to console. You can use Alt-F7 to switch back from console to the graphical user interface. Switch to console?
|
You can type antivir -h to see the options for running the
virus scanner software from the command line. Note: The keyboard layout
doesn't appear to match a U.S. keyboard layout; I had to hit the
"/" key (the one with the "?" on it) to get the dash character.
Command line options:
Usage is: antivir [options] [path[\*.ext]] [*.ext] where options are: --help .......... display this help text (abbreviation: -h or -?) --scan-mode=<mode> applies "extlist", "smart" or "all" scan methods: extlist scans files according to their filename extension, smart detects which files to scan from their name/content, all scans all files regardless of their name or content --allfiles ...... synonymous for --scan-mode=all --version ....... show version information --info .......... show list of recognized forms --update ........ update antivir --check ......... used with --update to check for updates --temp=<dir> .... specify the directory for temporary files --pid-dir=<dir> . specify the directory for PID files --home-dir=<dir> location of executable, VDF and key files -C <filename> ... name of configuration file -s .............. scan subdirectories --scan-in-archive files in archives will be extracted and scanned -z .............. synonymous for --scan-in-archive (scan in archives, too) --archive-max-size=N, --archive-max-recursion=N, --archive-max-ratio=N anti DoS feature: do not scan archive content which would exceed the given file size, nesting level or compression factor limits on extraction (0 means unlimited) --archive-max-count=N anti DoS feature: do not scan archive content which has more than N files in a recursion level --scan-in-mbox .. scan mailbox folders, too (might be time consuming!) --heur-macro .... enable macro heuristics --heur-nomacro .. disable macro heuristics --heur-level=N .. setup heuristics level: 0=off, 1-3=low-high -nolnk .......... do not follow symbolic links -onefs .......... do not cross file systems while following links -noboot ......... do not check any boot records -nombr .......... do not check any master boot records -nobreak ........ disable Ctl-C and Ctrl-Break -nodef ......... do only check the given file types (eg. *.DOC) -cf<filename> ... activate CRC check and name the database -cv ............. calculate CRC over the whole file length (default 16k) -cn ............. insert new files into the database -cu ............. recalculate CRC values and update the database -v .............. scan files completely (slower with possible false alerts) -nopack ......... do not scan inside packed files -e [-del | -ren] repair concerning files if possible [-del] non-repairable files will be deleted [-ren] non-repairable files will be renamed -ren ............ rename concerning files (*.COM->*.XXX,...) -del ............ delete concerning files --moveto=<dir> .. quarantine concerning files -dmdel .......... delete documents containing suspicious macros -dmdas .......... delete all macros if one appears to be suspicious -dmse ........... set exit code to 101 if any macro was found -r1 ............. just log infections and warnings -r2 ............. log all scanned paths in addition -r3 ............. log all scanned files -r4 ............. select verbose log mode -rs ............. select single-line alert messages -rf<filename> ... name of log file %d = day, %m = month, %y = year (two digits each) -ra ............. append new log data to existing file -ro ............. overwrite existing log file -q .............. quiet mode -lang[:|=]DE .... use German texts -lang[:|=]EN .... use English texts -once ........... run only once a day -if<dateiname> .. antivir uses the given ini file --with-<type> ... detect other (non-virus but unwanted) software, too; type may be e.g. "dial", "joke", "game", etc, there is a --with-alltypes shortcut --without-<type> like --with-<type>, but disables this type --alltypes ...... synonymous for --with-alltypes (obsolete) --alert-urls=<yes|no> print URL for more detailed information on alerts --warnings-as-alerts exit with a return code as if a concerning file had been found when warnings have been issued --exclude=<file> exclude files or directories from scan --log-email=<addr> send out scan report by email, too @<rspfile> ...... read parameters from the file <rspfile> with each option in a separate line list of return codes: 0: Normal program termination, nothing found, no error 1: Found concerning file or boot sector 2: An alert was found in memory 3: Suspicious file found 100: antivir only has displayed this help text 101: A macro was found in a document file 102: The option -once was given and antivir already ran today 200: Program aborted, not enough memory available 201: The given response file could not be found 202: Within a response file another @<rsp> directive was found 203: Invalid option 204: Invalid (non-existent) directory given at command line 205: The log file could not be created 210: antivir could not find a necessary dll file 211: Programm aborted, because the self check failed 212: The file antivir.vdf could not be read 213: An error occured during initialization 214: License key not found
When you are finished, you can click on the Shutdown button under Miscellaneous.
References: