

On Unix-like
systems, such as Linux and OS X, the list of authorized public keys is
usually stored in the home directory of the user that is allowed to log in
remotely via SSH in the file ~/.ssh/authorized_keys. The
file permissions for that file
must restrict write access to it to only the owner of the file, i.e., the
user's account, though, of course, the root account on a system can still
modify the file.
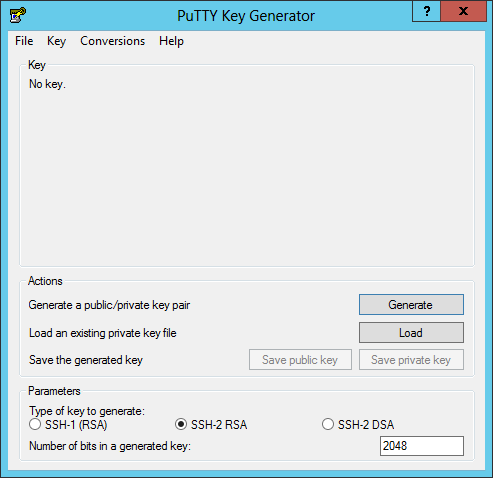
To create matching public and private keys with PuTTY, run the
puttygen program that comes with PuTTY.
Then click on the Generate button to generate matching public and private keys.
You will be requested to randomly move the mouse over the blank bar displayed in the window to ensure that there is a random element in the creation of the keys.
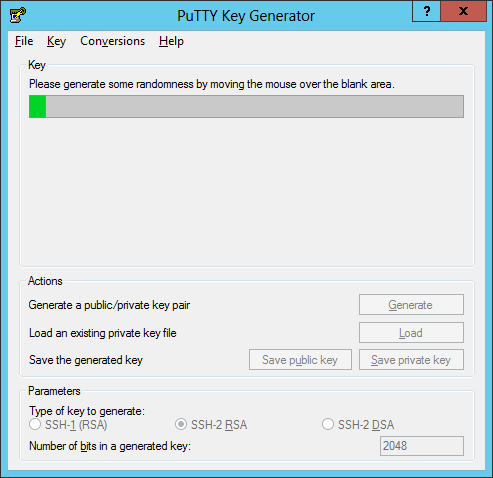
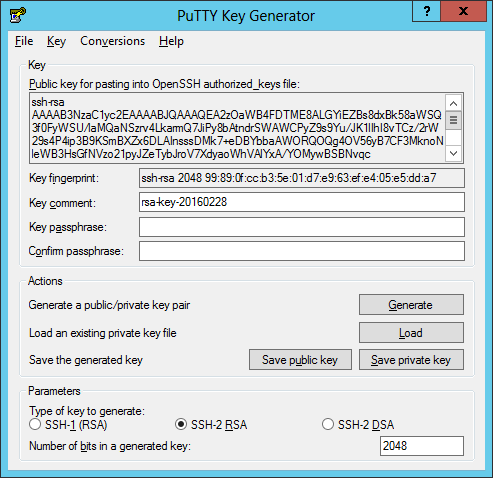
Keep moving the mouse about until the bar turns completely green. You will then see a public key displayed.
Type a key passphrase in the field by that name and type it again in the "confirm passphrase" field. This is akin to a password that you will use to access the private key you have created after you have saved it on your system. Make sure it is a strong passphrase, so that it can't be easily guessed by others, even by someone using a password guessing program that may be able to generate thousands of possible passwords per minute.
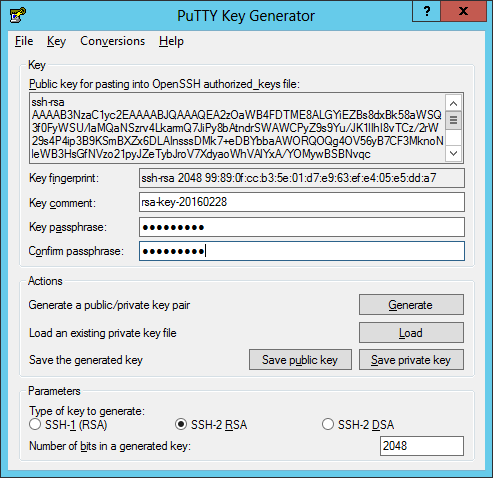
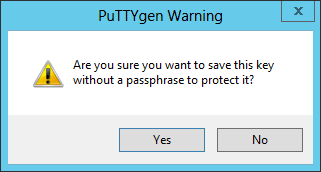
You can choose not to have a passphrase. If you don't set one, when you save the private key file, you will see a PuTTYgen warning asking "Are you sure you want to save this key without a passphrase to protect it?
You can replace the key comment, if you wish, to something that is
meaningful to you. E.g., if you were going to use it to connect to
example.com as jdoe, you could put "jdoe@example.com" there. By default,
the PuTTY Key Generator will use a comment similar to
rsa-key-20160228, indicating in this case that it is
an
RSA key generated on February 28, 2016.
Click on Save public key to save the public key. You can
pick whatever file name and extension you like for the public key file,
e.g. public_key1.txt. Then click on the Save
private key button and save the matching private key as well. That
file will get a .ppk extension by default. Store the file in some location that
others using the system won't be able to access.
You will need to place the public key on the server in
~/.ssh/authorized_keys. You can do that using the
vi editor, if
you are familiar with how to use that editor, with
vi ~/.ssh/authorized_keys. If you aren't familiar with the
editor, you can hit the i key when the editor starts to put
it into "insert" mode, then hit the Shift and Insert keys
simultaneously to paste the key. Then hit the Esc key to take the
editor out of "insert" mode. Then hit the colon (:) key and type wq
at the colon prompt you will see to write the file to disk and exit the
program. Or you can use another editor or transfer the public key file
to the SSH server by other means and save it to that location with that
file name. You will need to change the protection on the file so that only
the owner of the file has write access. Otherwise when you try to login,
after you provide the userid you will see "Server refused our key". E.g.,
the following permissions would result in that error message, since
"group" has write permission:
$ ls -l ~/.ssh/authorized_keys -rw-rw-r--. 1 jdoe jdoe 407 Feb 28 22:22 /home/jdoe/.ssh/authorized_keys
You can change the file permissions, granting access only to the owner by
issuing the chmod command chmod 600 ~/.ssh/authorized_keys from
the account for which you wish to use the public key.
If you are using a graphical user interface (GUI) on the SSH server end to import keys, such as the one provided by GoDaddy, you can copy the public key from the PuTTY Key Generator and paste it into the public key field in the GUI. If you are only going to be logging into the SSH server using the keys and not connecting outwards to another SSH server from that SSH server, you only need to provide a public key to the SSH server, keeping the private key only on the system you are running PuTTY. For the procedure for configuring a GoDaddy hosting account for SSH access, see GoDaddy SSH Access - Import PuTTY Key.
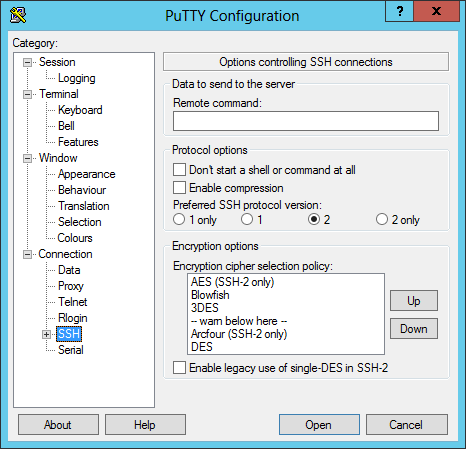
Once you've got the public key on the SSH server end, you should associate the private key with that SSH server within PuTTY, so open PuTTY and load the session for which you will use the private key you just created. After loading the session, click on SSH under Category.
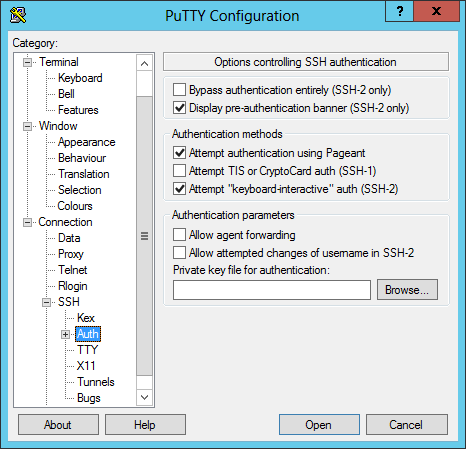
Clicking on the plus (+) sign next to it will expose a submenu of options; click on Auth.
Click on the Browse button and browse to where you stored the private key .ppk file. When you've located it, click on it to select it and then click on the Open button. You will then see the location for the file you selected in the "Private key for authentication" field.
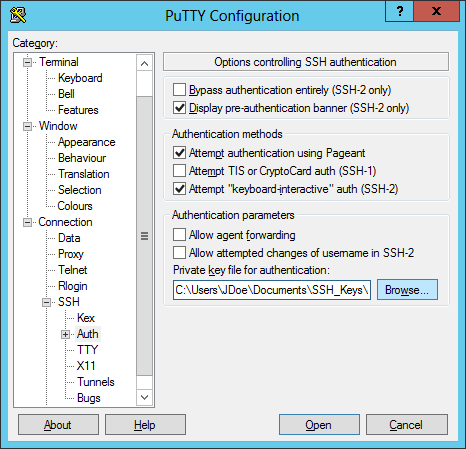
Then scroll up to Session at the top of the Category list and click on Save to save the modification you have made to the session. If you then click on Open and have the public key saved on the server already, you should be able to log in using the private key you generated.
If you set a passphrase, which is associated with the private key file,
after you provide a login id for the SSH server, you will see "Authenticating
with public key" followed by the key comment you provided when generating
the keys, e.g. rsa-key-20160228, and will then be prompted for
the passphrase you set, provided you set one. E.g.:
login as: jdoe Authenticating with public key "rsa-key-20160228" Passphrase for key "rsa-key-20160228": Last login: Sun Feb 28 20:30:11 2016 from 192.168.0.3 $
If you saved the private key file without a passphrase, you would be immediately logged in after providing the userid as shown below:
login as: jdoe Authenticating with public key "rsa-key-20160228" Last login: Sun Feb 28 20:33:41 2016 from 192.168.0.3 $