When checking the firewall settings on a Windows XP Service Pack 2 system tonight, I found several anomalous firewall rules. The system is running the Windows XP firewall.
When I checked the firewall openings with the netsh firewall show
state command, I didn't see anything unusual.
C:\>netsh firewall show state Firewall status: ------------------------------------------------------------------- Profile = Domain Operational mode = Enable Exception mode = Enable Multicast/broadcast response mode = Enable Notification mode = Enable Group policy version = Windows Firewall Remote admin mode = Enable Ports currently open on all network interfaces: Port Protocol Version Program ------------------------------------------------------------------- 135 TCP IPv4 (null) 137 UDP IPv4 (null) 139 TCP IPv4 (null) 138 UDP IPv4 (null) 9370 UDP IPv4 C:\Program Files\Logitech\Desktop Messenger\8876480\Pr ogram\LogitechDesktopMessenger.exe 3389 TCP IPv4 (null) 445 TCP IPv4 (null) 22 TCP IPv4 C:\Program Files\Network\OpenSSH\usr\sbin\sshd.exe
Nor did I see anything unusual when I issued the command
netsh firewall show portopening.
C:\>netsh firewall show portopening Port configuration for Domain profile: Port Protocol Mode Name ------------------------------------------------------------------- 22022 TCP Enable OpenSSH 139 TCP Enable NetBIOS Session Service 445 TCP Enable SMB over TCP 137 UDP Enable NetBIOS Name Service 138 UDP Enable NetBIOS Datagram Service 3389 TCP Enable Remote Desktop Port configuration for Standard profile: Port Protocol Mode Name ------------------------------------------------------------------- 139 TCP Enable NetBIOS Session Service 445 TCP Enable SMB over TCP 137 UDP Enable NetBIOS Name Service 138 UDP Enable NetBIOS Datagram Service 3389 TCP Enable Remote Desktop
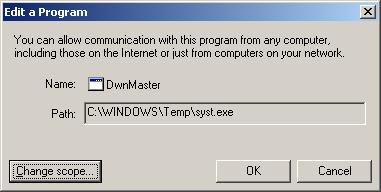
However, when I went to the GUI for configuring the firewall to correct an mistake I noticed in the firewall configuration, I saw DwnMaster listed. I didn't know what that program was nor why it needed a firewall rule.

Double-clicking on DwnMaster showed that the program associated with the firewall rule was syst.exe in C:\WINDOWS\Temp.
When I checked to see if syst.exe was running, I didn't see evidence of it running.
C:\>tasklist /fi "imagename eq syst.exe" INFO: No tasks running with the specified criteria.
And when I checked for the existence of the file, however, though I found it, it was only zero bytes in length. I am presuming that it was nullified during an antivirus or antispyware scan of the system.
C:\>dir c:\windows\temp\syst.exe
Volume in drive C has no label.
Volume Serial Number is 909B-3E78
Directory of c:\windows\temp
02/02/2007 03:32 AM 0 syst.exe
1 File(s) 0 bytes
0 Dir(s) 57,556,082,688 bytes free
Looking at the "allowed programs" list for the firewall, I noticed another unusual entry, C:\win.com.
C:\>netsh firewall show allowedprogram Allowed programs configuration for Domain profile: Mode Name / Program ------------------------------------------------------------------- Enable Remote Assistance / C:\WINDOWS\system32\sessmgr.exe Enable DwnMaster / C:\WINDOWS\Temp\syst.exe Enable TCP / C:\WIN.COM Enable Logitech Desktop Messenger / C:\Program Files\Logitech\Desktop Messenge r\8876480\Program\LogitechDesktopMessenger.exe Allowed programs configuration for Standard profile: Mode Name / Program ------------------------------------------------------------------- Enable restorea0 / c:\windows\system32\restorea0.exe Enable Remote Assistance / C:\WINDOWS\system32\sessmgr.exe Enable Logitech Desktop Messenger / C:\Program Files\Logitech\Desktop Messenge r\8876480\Program\LogitechDesktopMessenger.exe
The name given to it was TCP, apparently in an attempt to make it less likely to stand out as possible malware.

But I wouldn't expect to find a win.com file in the root directory of a Windows XP system.

It was also a zero byte file when I checked for its existence, however, so may also have been nullified by a previous scan of the system with antivirus or antispyware software.
C:\>dir c:\win.com
Volume in drive C has no label.
Volume Serial Number is 909B-3E78
Directory of c:\
02/09/2007 02:47 AM 0 WIN.COM
1 File(s) 0 bytes
0 Dir(s) 57,555,771,392 bytes free
Another allowed program that looked suspicious was restorea0 in c:\windows\system32\. But when I looked for it, I did not see it on the system. So it may have been removed completely by antivirus or antispyware software previously. At FKIYY.EXE Spyware Remove, I found it listed as one of many alternative names associated with malware detected by Prevx.
At SYST.EXE Spyware Remove, Prevx lists syst.exe as being associated with Trojan Downloader Small yt. At WIN.COM Spyware Remove, win.com is linked to Adware Virtumonde

